top of page
All Posts


AI Prototype: Non-Human Identity (NHI) Risk Analyzer
The Problem Most Enterprises Miss While user identities are heavily governed, non-human identities (NHIs)—such as service accounts and API keys—often remain overlooked. n many environments, I’ve observed: Service accounts running for years without review API keys with high privileges and no clear ownership Credentials that are rarely used—but never revoked Unlike human identities, these do not trigger obvious alerts. They don’t fail loudly—they quietly expand your attack surf
Madhukeshwar Bhat
20 hours ago2 min read

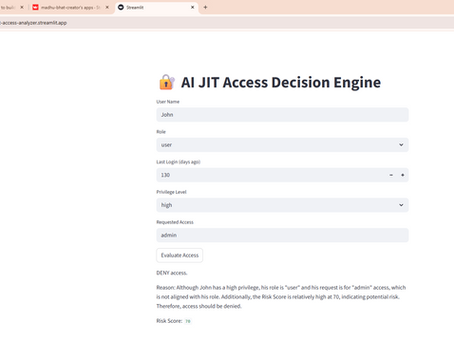
AI Prototype: Just-in-Time Identity Access Decision Engine
The Problem I Kept Seeing In most enterprises I’ve worked with, identity risk doesn’t fail loudly—it silently accumulates. Users retain access long after they need it Privileged roles remain active despite inactivity Access reviews happen periodically, not when risk actually emerges Traditional IAM systems try to solve this using: Static rules Periodic certifications Manual reviews But the reality is simple: Risk is dynamic — while controls are static The Idea I wanted to exp
Madhukeshwar Bhat
21 hours ago2 min read


Why Data Governance Fails at Scale: It’s Not Data, It’s Ownership
YouTube Link for short talk : https://youtu.be/koNNzeSbV8s Many organizations treat data problems as technology problems. In reality, they are ownership and control problems. In areas like Data Office and Anti-Financial Crime, data doesn’t fail because it doesn’t exist; it fails because it isn’t clearly owned, governed, or consistently controlled. If we want data to scale, we need to move beyond tools and focus on the systems around data: ownership, decision rights, and contr
Madhukeshwar Bhat
1 day ago1 min read


AI Prototype – Identity Access Risk Analyzer
The Problem I Kept Seeing In most enterprises I’ve worked with, identity risk doesn’t fail loudly — it silently accumulates. Users retain access long after they need it.Privileged roles remain active despite inactivity.And risk reviews happen periodically, not when risk actually emerges. Traditional IAM systems try to solve this using: Static rules Periodic certifications Manual reviews But the reality is: Risk is dynamic — while controls are static The Idea I wanted to explo
Madhukeshwar Bhat
2 days ago2 min read


Identity Will Become the Primary Signal for AI-Driven Security
As enterprises move toward AI-driven security models, traditional signals like network location or device posture are becoming less reliable in increasingly distributed environments. What remains consistent across every interaction is identity . Every action, whether initiated by a human, service, workload, or AI agent, ultimately occurs through an identity. This means identity data, behavior patterns, and contextual authorization signals will increasingly drive security deci
Madhukeshwar Bhat
Apr 181 min read


Shared Responsibility Is Often Shared Confusion
The cloud’s shared responsibility model is well understood in theory: providers secure the infrastructure while organizations secure their workloads, identities, and data. In practice, however, shared responsibility often becomes shared confusion . Responsibilities get spread across security, platform, and application teams, and assumptions form about who owns what. The result is not a lack of tools or controls, it’s gaps in operational ownership. The organizations that manag
Madhukeshwar Bhat
Apr 41 min read


The Accountability Shift in Cybersecurity
Enterprises have invested heavily in strengthening security controls over the past decade. Yet in many complex environments, the real constraint is no longer control coverage — it is ownership clarity. In this video, I share why the next phase of cyber maturity will depend on shifting focus from adding safeguards to strengthening accountability around the controls we already have. Link to You Tube talk: https://youtu.be/4E28qV2OGqY #CyberSecurity#Leadership#EnterpriseSecuri
Madhukeshwar Bhat
Mar 211 min read


The Illusion of Control in Enterprise Security
In enterprise security, the presence of controls often creates a reassuring picture. But real resilience is shaped by how those controls perform in the complexity of day-to-day operations. In this short video, I reflect on the growing gap between perceived control and operational reality — and why the next phase of cyber maturity will depend more on accountability and system behavior than on control coverage alone. Youtube link for the talk: https://youtu.be/ZJGRaOuiyHE
Madhukeshwar Bhat
Mar 71 min read


Why Standardization Breaks in Regulated Enterprises
Standardization rarely fails because the model is wrong — it fails because reality is more heterogeneous than we admit. In regulated enterprises especially, progress comes not from denying exceptions, but from governing them well. A short reflection using IAM onboarding as one example. Here is the link to YouTube version of my Talk: https://youtu.be/3wYGjQsS2KM #Transformation #EnterprisePlatforms #Governance #IAM
Madhukeshwar Bhat
Feb 141 min read


Why AI Fails Like IAM
There’s a strong sense of urgency around AI adoption in enterprises — but we’ve been here before. Identity and Access Management promised security and control, yet struggled at scale not because of technology limitations, but because adoption, ownership, and operating models were underestimated. AI is walking into the same enterprise realities. In this short talk, I explore why AI success will depend less on models and more on leadership decisions — clarity of ownership, deci
Madhukeshwar Bhat
Jan 311 min read


Why Platforms Fail at Adoption
When enterprise platforms struggle, the conversation often turns to tools and architecture. In reality, most platforms don’t fail because of technology — they fail because adoption is treated as an afterthought. In complex, regulated environments, adoption depends less on features and more on clarity of ownership, incentives, and decision rights. In this short talk, I share why enterprise platform adoption is fundamentally a leadership challenge. The focus isn’t on choosing b
Madhukeshwar Bhat
Jan 181 min read


What Scaling GCCs Teach Us About Platform Ownership and Risk
As Global Capability Centers scale, the conversation inevitably shifts from delivery to ownership. What becomes clear very quickly is that many risk challenges aren’t caused by technology gaps, but by unclear decision rights, fragmented accountability, and operating models that haven’t evolved with scale. In this short talk, I reflect on what scaling GCCs teach us about platform ownership and risk. The focus isn’t on adding more controls, but on designing ownership models tha
Madhukeshwar Bhat
Jan 181 min read


Why Cybersecurity Is a Leadership Decision, Not a Technology One
Cybersecurity conversations often get trapped in tools, controls, and incidents. But in large, complex organizations, the real challenge is rarely technological. It’s about how leaders make decisions under uncertainty — how they balance speed, cost, user experience, and risk. When those trade-offs aren’t clearly owned, teams compensate with friction, delivery slows down, and security becomes reactive. In this short talk, I share why I believe cybersecurity is fundamentally a
Madhukeshwar Bhat
Dec 20, 20251 min read


The Future of Cloud Security: From Automation to AI
I had the opportunity to lead a thought-provoking conversation with three exceptional leaders — Nitish Tiwari (Palo Alto Networks) , Harinderjeet Singh Walia (IAF Veteran & Cyber Expert) , and Dr. Ramkumari Harisankar Iyer (CISO & CIO) — on how cloud security is being reshaped by automation, AI, and emerging quantum technologies. We explored insights across: AI-driven detection, response & predictive security Automation powering scalable Zero Trust Adversarial AI and the nex
Madhukeshwar Bhat
Nov 29, 20251 min read


AI Is Changing Security. Are We Ready?
Thoroughly enjoyed being part of a thought-provoking panel discussion last week on “Securing the AI Stack — from Code to Identity” during CyBe Meet-up. We explored some deep questions, including: How do modern identity frameworks like Just-in-Time access and Zero Trust extend into the AI ecosystem? What new attack surfaces emerge with AI-driven applications compared to traditional cloud apps? Do we need a new concept of AI identity for autonomous agents interacting with h
Madhukeshwar Bhat
Nov 1, 20251 min read


Policy-Based Access Control (PBAC) — The Next Step in Identity Security
Policy-Based Access Control (PBAC) is transforming how organizations manage authorization by shifting from static roles to dynamic,...
Madhukeshwar Bhat
Oct 11, 20251 min read


Leveraging AI for Smarter Cybersecurity: Mini Reconciliation Utility & IAM Policy Explainer
I recently built two small but powerful AI-driven tools for Cybersecurity: 🔹 Mini Reconciliation Utility – compares two Excel sheets...
Madhukeshwar Bhat
Sep 10, 20251 min read


Is Quantum Computing an opportunity or a threat to Cybersecurity?
Is quantum computing an opportunity or threat to cyber security? I would say both! Quantum computing is an emerging field. While this is...
Madhukeshwar Bhat
Sep 6, 20251 min read
🔐 Identity Is the New Perimeter
Today, attackers don’t break in—they log in.In this short Cybertalk, I am sharing my views on why identity is now your #1 security...
Madhukeshwar Bhat
Aug 23, 20251 min read


Human factors in Cybersecurity
While we invest heavily in tech, it's human behavior that causes over 80% of cyber incidents. From culture to accountability, leaders...
Madhukeshwar Bhat
Aug 9, 20251 min read
bottom of page